Archive for the ‘Info Security or Ethical Hacking Tools’ Category
Retina Network Security Scanner by BeyondTrust
Unlike most of the software applications reviewed here, Retina Network Security Scanner by BeyondTrust is not available as freeware. As it is a highly capable and fully-featured security vulnerability scanner, it is distributed as commercial software. The license pricing for Retina is $1,200. The license is actually one year subscriptions as Retina will not function after the one-year period is over unless you renew.
While your subscription period is valid, you can download and install updates for Retina. These updates take two forms: patches for the Retina scanner itself, and vulnerability definition updates that allow Retina to recognize the latest vulnerabilities and exploits. In this way, Retina must be kept up to date in the same way that antivirus scanners do.
Retina must be installed on the Windows operating system; supported versions of Windows run from Windows 2000 to Windows Server 2012. Retina can scan all networked hosts regardless of operating system, however.
Retina is one of the main network scanners used in the Department of Defense (DoD). In January of 2013 the DoD continued its long relationship with BeyondTrust (formerly known as eEye) by renewing its vulnerability management contract between DISA and BeyondTrust.
Retina interface
When you launch Retina you will see the main user interface as depicted below.
Usage options are divided among four interface tabs: Discover, Audit, Remediate, and Report.
Reset Windows passwords with Offline NT Password & Registry Editor
The Offline NT Password & Registry Editor is a small Linux boot disk that you can use to change or delete Windows passwords outside of the Windows OS environment for local accounts. This can be useful if you forget your Windows password or the password belonging to the Administrator account. This utility can enable you to change or delete passwords, but it cannot tell you what the password for an account actually is. As such it is not appropriate to label Offline NT Password & Registry Editor as a ‘password recovery tool’; it’s a password editor, just like the name says.
It is compatible with Windows 3.x, Windows 95/98/ME, Windows NT, Windows 2000, Windows XP, Windows Server 2003, Windows Vista, Windows 7, and Windows Server 2008.
Please note that the Offline NT Password & Registry Editor (‘Offline’) home page states: “If password is reset on users that have EFS encrypted files, and the system is XP or newer, all encrypted files for that user will be UNREADABLE and cannot be recovered unless you remember the old password again“.
Also note that Offline cannot be used to change or reset Active Directory passwords.
Offline’s versioning is done using release dates. The version used in this tutorial is 110511 (for 11 May 2011).
How to use it
First, download the installation ‘cd******.zip’ file from the website above and extract it locally. Burn the resulting .iso file to a CD-ROM. If you plan to boot to a USB drive, download the ‘usb********.zip’ file and extract its contents to the drive.
Second, insert the CD or USB drive into the computer and reboot it. Before the Windows OS loads (while the manufacturer’s screen is briefly displayed), hit the appropriate key (usually one of the twelve ‘F’ keys) to enter the boot device manager where you can specify a device to boot to (overriding the default device, which is almost always C:\ on the internal hard drive).
Your computer will load the contents of the Offline CD or USB drive. When it is finished you will be prompted as follows.
SoftPerfect Network Scanner
SoftPerfect Network Scanner is one of the most popular free programs in Download.com’s Network Tools category. It offers many features and options for detecting and probing network hosts. It is a portable application (it does not need to be installed; you just double-click netscan.exe to launch it).
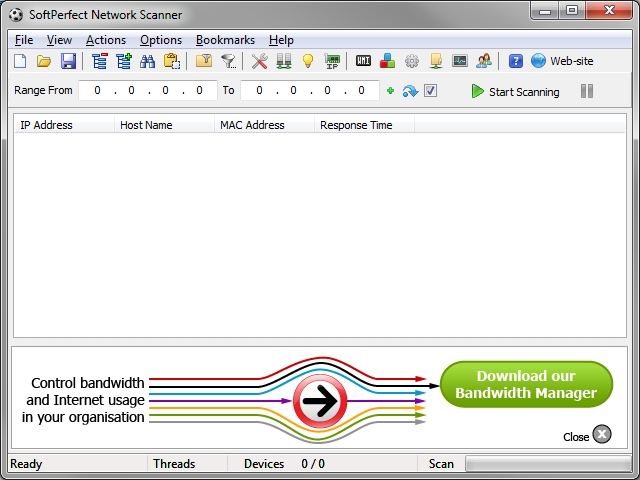
Softperfect Network scanner v5.5.6 main interface
Send spoofed emails with telnet
You can send spoofed emails (i.e., emails with a fake source address) if you can establish a telnet session with an email server. (Before continuing, go here if you need to brush up on your telnet knowledge).
If you don’t know the host name of an email server, you’ll have to find one using a utility like dig or nslookup.
For dig, the command to find email servers for a domain (e.g., hotmail.com) is:
dig @[DNS_server_name_or_IP] hotmail.com MX
The output of this command is as follows:
; <<>> DiG 9.3.2 <<>> @208.67.222.222 hotmail.com MX ; (1 server found) ;; global options: printcmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17095 ;; flags: qr rd ra; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 0 ;; QUESTION SECTION: ;hotmail.com. IN MX ;; ANSWER SECTION: hotmail.com. 3600 IN MX 5 mx3.hotmail.com. hotmail.com. 3600 IN MX 5 mx4.hotmail.com. hotmail.com. 3600 IN MX 5 mx1.hotmail.com. hotmail.com. 3600 IN MX 5 mx2.hotmail.com. ;; Query time: 157 msec ;; SERVER: 208.67.222.222#53(208.67.222.222) ;; WHEN: Sat Dec 31 19:28:50 2011 ;; MSG SIZE rcvd: 109
.
As you can see, the four email servers for the domain hotmail.com are mx1.hotmail.com, mx2, etc.
How to block malware with the hosts file
On the Microsoft Most Valuable Players (MVPs) website you can download a custom hosts file to prevent unwanted connections to thousands of websites that distribute malware in its many forms – adware, spyware, etc. How does this work? First let’s review the hosts file and what it does.
The hosts file exists in both Windows and Linux/Unix. It is a simple text file that maps IP addresses to host names, thus bypassing the functionality of name resolution courtesy of DNS servers. The hosts file is simply named ‘hosts’ with no file extension such as .txt. In Linux and Unix, hosts can be found in /etc/hosts. In modern Windows operating systems it is located in %SystemRoot%\system32\drivers\etc\hosts (%SystemRoot% is usually C:\).
The default hosts in Windows 7 looks like this:
# Copyright (c) 1993-2009 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
.
As you can see, the two bottom lines linking the localhost name with the loopback address 127.0.0.1 in IPv4 and with ::1 in IPv6 are commented out by default. In previous versions of Windows these lines were not commented out. The DNS resolver in Windows 7 apparently handles the localhost/127.0.0.1 translation.
Spoofing MAC addresses in Linux and Windows
Recall that each network adapter (whether wired or wireless) has a hard-coded (“burned in”) Media Access Control (MAC) address that uniquely identifies the adapter on the local network to which it is connected. MAC addresses are 48-bit values comprised of twelve hexadecimal characters (0-9 and A-F). The twelve characters are separated into six pairs or octets. The first three octets are called the organizationally unique identifier (OUI) which identifies the manufacturer of the network adapter and the last three octets uniquely identify the adapter itself.
Many networks (WLANs in particular) enforce access restrictions based on host MAC addresses. To bypass this MAC filtering you can fake or “spoof” your own MAC address (you will need a known permitted MAC address to change to, obviously).
Linux
Modern operating systems give you the ability to bypass the burned in MAC address in favor of an arbitrary one that you specify. In Linux this is a simple process. To temporarily (until next reboot) change your MAC address, enter the following commands as root (where eth0 is your network interface card).
# ifconfig eth0 down
# ifconfig eth0 hw ether 00:70:59:CE:f1:20 (or whichever value you choose)
# ifconfig eth0 up
To use the new ip command (which replaces the deprecated ifconfig):
# ip link set dev [interface] address [mac_addr]
When you reboot, Linux will revert back to using the network interface card’s (NIC’s) normal MAC address. To make your spoofed MAC address “permanent”, in Red Hat/Fedora/CentOS you can edit /etc/sysconfig/network-scripts/ifcfg-eth0 (replace ‘eth0’ with your interface) and add:
MACADDR=21:22:44:34:23:27 (or whichever value you prefer).
HackerStorm Open Source Vulnerability Database
The HackerStorm Open Source Vulnerability Database (OSVDB) tool is a web-based utility (runs in a web browser) that enables you to research vulnerabilities associated with various software companies, such as Microsoft, Mozilla, Red Hat, etc. You simply download the tool and the associated vulnerability database and you use the Flash-based graphical user interface (GUI) to get the details on vulnerabilities based on software vendor.
Unfortunately this project appears to have fallen by the wayside as it has not been updated in quite some time. The latest HackerStorm database dates from 30 April 2010. The HackerStorm blog has only been updated once since 9 May 2009. Currently the latest vulnerability for Mozilla products in the OSVDB dates to March 2010; the latest vulnerability for Red Hat dates to August 2009. Clearly there have been more exploits for Mozilla and Red Hat products discovered since these dates. Therefore bear in mind that at the present, the HackerStorm OSVDB will not display vulnerabilities that were discovered after April 2010.

HackerStorm OSVDB v1.1 main interface






You must be logged in to post a comment.